While this guide provides a framework for compliance, the complexities of HIPAA and state privacy laws require expert guidance.
As a personal injury attorney, you carry a dual responsibility that is both profound and challenging. You must be a zealous advocate for your clients, fighting to secure the compensation they deserve. At the same time, you are the guardian of their most sensitive personal data, including detailed medical records that are protected by federal law. Navigating this intersection of legal discovery and medical privacy law requires precision, diligence, and a clear understanding of your obligations under the Health Insurance Portability and Accountability Act (HIPAA).
The stakes for getting this wrong are higher than ever. Data security is no longer a concern just for large corporations; law firms of all sizes are prime targets for cyberattacks and accidental breaches. According to the American Bar Association, nearly 30% of law firms have experienced a security breach. The financial fallout can be catastrophic, with the average cost of a data breach for professional services firms climbing to $5.08 million in 2024. This guide will provide a straightforward, step-by-step protocol for requesting, receiving, and transmitting client medical records without violating HIPAA regulations, helping you protect both your clients and your practice.
Why HIPAA Compliance is Non-Negotiable for Personal Injury Attorneys
Before diving into the “how,” it is critical to understand the “why.” HIPAA is not merely a set of best practices; it is a federal mandate with significant legal and financial penalties for non-compliance. For personal injury attorneys, who regularly handle a high volume of medical information, a foundational knowledge of HIPAA’s core components is essential for building a defensible security posture and maintaining client trust.
Understanding Protected Health Information (PHI)
At the heart of HIPAA is the concept of Protected Health Information (PHI). In simple terms, PHI is any health information that can be linked to a specific individual and is used, maintained, or transmitted by a healthcare provider or their business associate. This definition is broad and covers more than just a patient’s diagnosis. Clear examples of PHI you frequently encounter include medical charts, billing information from healthcare providers, MRI films and other diagnostic images, and specific CPT or ICD-10 diagnostic codes. Any document containing one of these identifiers along with a patient name or social security number is considered PHI and must be protected accordingly.
The HIPAA Privacy Rule vs. The Security Rule
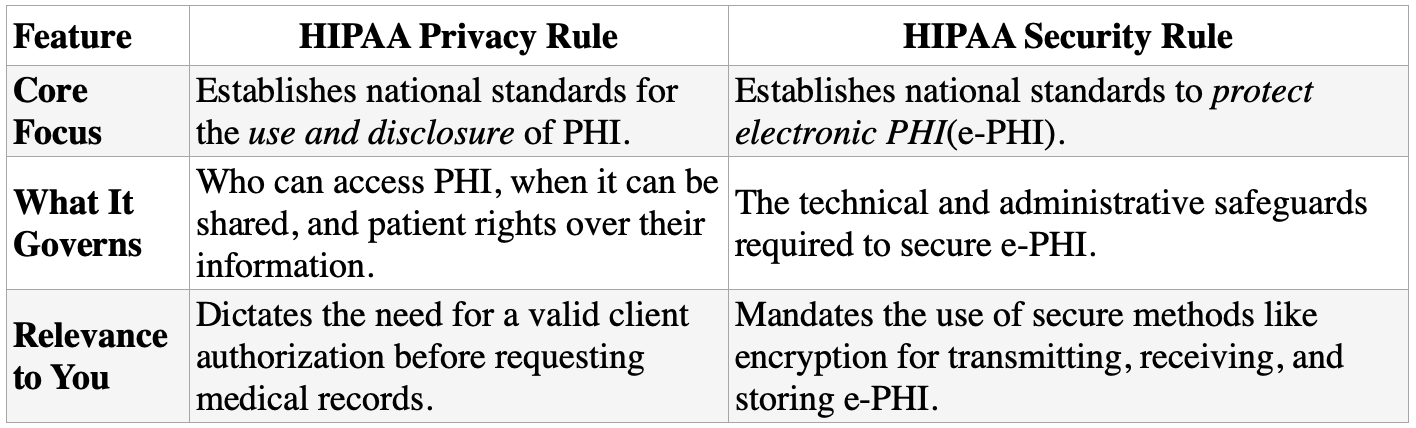
To ensure compliance, you must understand the distinction between HIPAA’s two most important components: the Privacy Rule and the Security Rule. While they work together, they govern different aspects of data protection. The Privacy Rule sets the standards for who can use and share PHI, while the Security Rule dictates the safeguards required to protect that data in its electronic form (e-PHI).
The Rising Tide of Enforcement
Federal regulators are signaling a clear shift toward stricter enforcement, moving beyond basic compliance checks to a more holistic evaluation of a firm’s security culture. According to legal analysis of 2025’s trends, regulators like the Department of Health and Human Services’ Office for Civil Rights (OCR) are expanding their scrutiny to include cybersecurity hygiene, vendor oversight, and incident response playbooks. This means that simply having policies on paper is no longer enough. You must be able to demonstrate that you are actively implementing, testing, and training your staff on these security protocols, as the standards for compliance are only getting more stringent.
A Step-by-Step Protocol for Handling PHI in 2026
A secure document workflow is your firm’s first line of defense against a data breach. By following a consistent and documented protocol, you can minimize risk and demonstrate due diligence in the event of an audit. This chronological guide breaks down the essential steps for managing PHI from initial client intake to sharing records with third parties.
Step 1: Secure a Valid HIPAA Authorization
The entire process begins with obtaining proper consent from your client. It is a common mistake to assume that a standard medical release form included in your client retainer agreement is sufficient. Under HIPAA, an authorization to release PHI must be a standalone document that is highly specific, detailing exactly what information will be shared, which providers are authorized to release it, who will receive it, and for what specific purpose (e.g., for use in a personal injury claim). Vague or overly broad authorizations can be deemed invalid, so clarity and specificity are paramount.
Step 2: Request Medical Records Securely
Once you have a valid authorization, you must use a secure method to request the records. Traditional methods like postal mail or standard, unencrypted fax machines are fraught with vulnerabilities. Human error remains a leading cause of data breaches in the legal field. A 2024 analysis found that 37% of data breaches in the UK legal sector were caused by sharing data with the wrong person via email or post. Using a secure digital portal or a compliant electronic method to submit requests minimizes the risk of documents being lost, stolen, or intercepted.
Step 3: Receive and Store PHI with Fortified Security
Your responsibility does not end once the records are in your possession. You must ensure that all client PHI is stored in a secure environment. Key practices include implementing role-based access control, which limits access to sensitive files to only those staff members who absolutely need it for their job functions. Furthermore, all data must be encrypted “at rest”—meaning the files are encrypted while stored on your server, cloud storage, or hard drive. This aligns with the OCR’s recent focus, as highlighted in its January 2026 Cybersecurity Newsletter, which reminds covered entities about the importance of “system hardening” measures to protect stored data.
Step 4: Transmit PHI to Third Parties with Confidence
Perhaps the most critical and high-risk step is sharing PHI with insurance adjusters, expert witnesses, co-counsel, or other entities involved in the case. Sending these sensitive documents as standard attachments to an unencrypted email is a direct violation of the HIPAA Security Rule and exposes your firm to significant liability. This is where a modern solution like an online fax service becomes essential.
For legal professionals who need to transmit sensitive records, using a service specifically designed for security and compliance is critical. A leading choice in this space is iFax, which offers a HIPAA-compliant online fax solution built to meet the rigorous demands of the legal and healthcare industries. It directly addresses the key vulnerabilities of traditional methods by providing 256-bit end-to-end encryption for all documents, both in transit and at rest. This ensures that from the moment you send a client’s medical file to the moment it’s received, it’s protected by military-grade security.
The iFax platform also provides a clear audit trail, offering confirmation of delivery and a log of all transmissions, which is invaluable for demonstrating due diligence and compliance. Furthermore, its user-friendly interface, accessible across web, desktop, and mobile platforms, allows legal teams to integrate secure faxing into their workflow without the friction of outdated hardware. This combination of robust security, ease of use, and multi-platform accessibility is why a significant number of attorneys—42% of solo attorneys and 40% of lawyers in small firms as of 2023—are adopting electronic fax software to manage their secure document transmission needs effectively.
Building a Culture of Security in Your Practice
Technology is a critical tool, but a truly defensible security posture is built on a foundation of sound policies, continuous training, and an organization-wide commitment to protecting client data. Moving beyond the document workflow, these best practices can help your firm create a comprehensive compliance strategy that withstands regulatory scrutiny.
Implement a Formal Data Security Policy
Your firm should have a written, accessible data security policy that serves as the official guide for all employees. This document should clearly outline the firm’s rules for handling PHI, specify the approved technologies and methods for transmitting data, and detail the step-by-step procedure for responding to a suspected data breach. A formal policy removes ambiguity and ensures everyone on your team understands their obligations.
Prioritize Continuous Staff Training
Even the most advanced security software cannot prevent a breach caused by an employee clicking on a phishing link or improperly sharing a file. Regular, ongoing training is essential to ensure every team member, from paralegals to partners, understands their role in protecting client data. Training should cover how to recognize common cyber threats like phishing, the firm’s specific data security policies, and the consequences of non-compliance with HIPAA.
Essential Security Measures for Every Firm
Beyond policies and training, certain technical controls are now considered non-negotiable baseline measures for any firm handling PHI. These controls are frequently cited in OCR enforcement actions and are critical to demonstrating a good-faith effort to comply with HIPAA.
- Enforce Multi-Factor Authentication (MFA): As highlighted by federal enforcement trends, MFA is a mandatory baseline for securing access to any system containing PHI, including email, case management software, and cloud storage.
- Encrypt All Devices: Ensure that all laptops, smartphones, and servers that store or access client data are fully encrypted to protect information if a device is lost or stolen.
- Execute Business Associate Agreements (BAAs): Before using any third-party vendor that will handle PHI (including case management software or an online fax provider), you must have a signed BAA in place. This is a legal requirement under HIPAA that contractually binds your vendor to protect the PHI they handle on your behalf.
- Develop an Incident Response Plan: Know the exact steps to take in the event of a data breach. Regulators are increasingly examining these plans during investigations to assess a firm’s preparedness and response capability.
- Maintain Comprehensive Audit Logs: Use systems that automatically track who accesses, modifies, or transmits PHI and when. These logs are your first line of defense in a compliance audit, providing a verifiable record of your firm’s data handling practices.
Navigating Medical Privacy with Confidence
For personal injury lawyers in 2026, protecting client data is not an administrative task—it is a core professional duty. HIPAA compliance is a fundamental obligation that requires a deep understanding of the rules, a documented and secure workflow for managing PHI, and the right technology to mitigate risks. By adopting a proactive approach that combines clear policies, ongoing training, and modern, compliant tools, you can navigate the complexities of medical records privacy with confidence.
While this guide provides a framework for compliance, the complexities of HIPAA and state privacy laws require expert guidance. The most prudent next step is to consult with a legal technology or cybersecurity expert to ensure your firm’s practices are fully compliant and secure.


Join the conversation!